Tagged: AI, Attack Surface, Cloud Threats, MSOC in the Philippines, Risk, Vulnerabilities
- This topic has 0 replies, 1 voice, and was last updated 1 week, 6 days ago by
Rameses Quiambao.
- AuthorPosts
- April 23, 2026 at 4:28 pm #1958
Rameses Quiambao
ParticipantAs organizations accelerate their adoption of cloud and AI technologies, the cybersecurity landscape continues to evolve but not always in the way many expect. The Cloud Threats Retrospective 2026 by Wiz highlights a critical reality: while innovation is moving fast, attackers are still succeeding familiar, long-standing weaknesses.
Rather than relying on entirely new techniques, threat actors are scaling proven methods, exploiting systemic gaps, and leveraging AI to increase efficiency. Understanding these trends is essential for organizations aiming to secure modern cloud environments.
The State of Cloud Threats in 2025
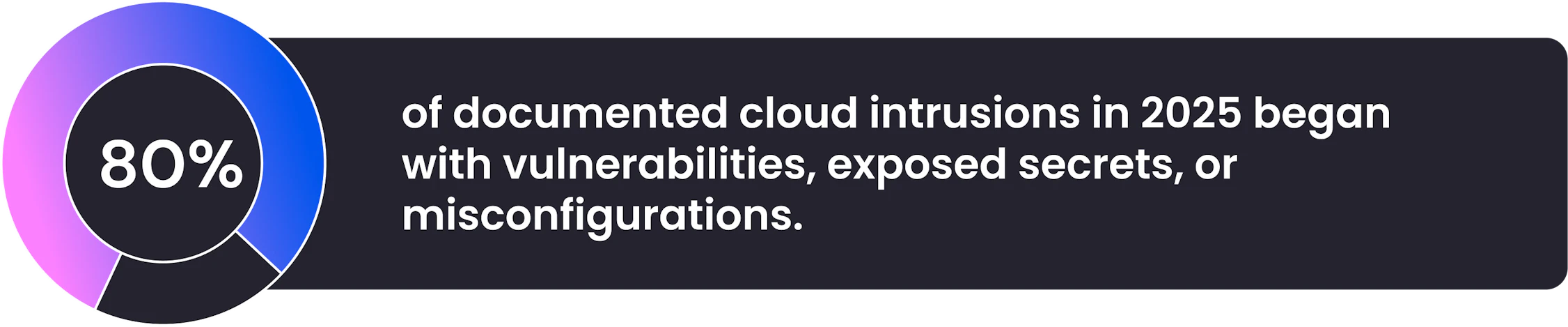
The 2026 retrospective reveals a clear pattern most successful cloud attacks did not depend on advanced zero-day exploits or highly sophisticated techniques. Instead, attackers continued to exploit:
Misconfigurations
Exposed secrets (API keys, credentials)
Known vulnerabilitiesThese are not new problems. However, their impact has grown significantly due to the scale, complexity, and interconnected nature of modern cloud environments.
Classic Cloud Risks Still Dominate

Despite advancements in cloud security tools, traditional weaknesses remain the primary entry point for attackers.Key Insight:
Organizations are still being compromised through:
Poorly configured storage and services
Unpatched systems
Hardcoded or leaked credentialsThis highlights a fundamental issue: security hygiene gaps continue to outweigh cutting-edge threats.
In many cases, the challenge is not awareness but execution. As cloud environments grow, maintaining consistent configurations and patching becomes increasingly difficult, especially without automation and centralized visibility.
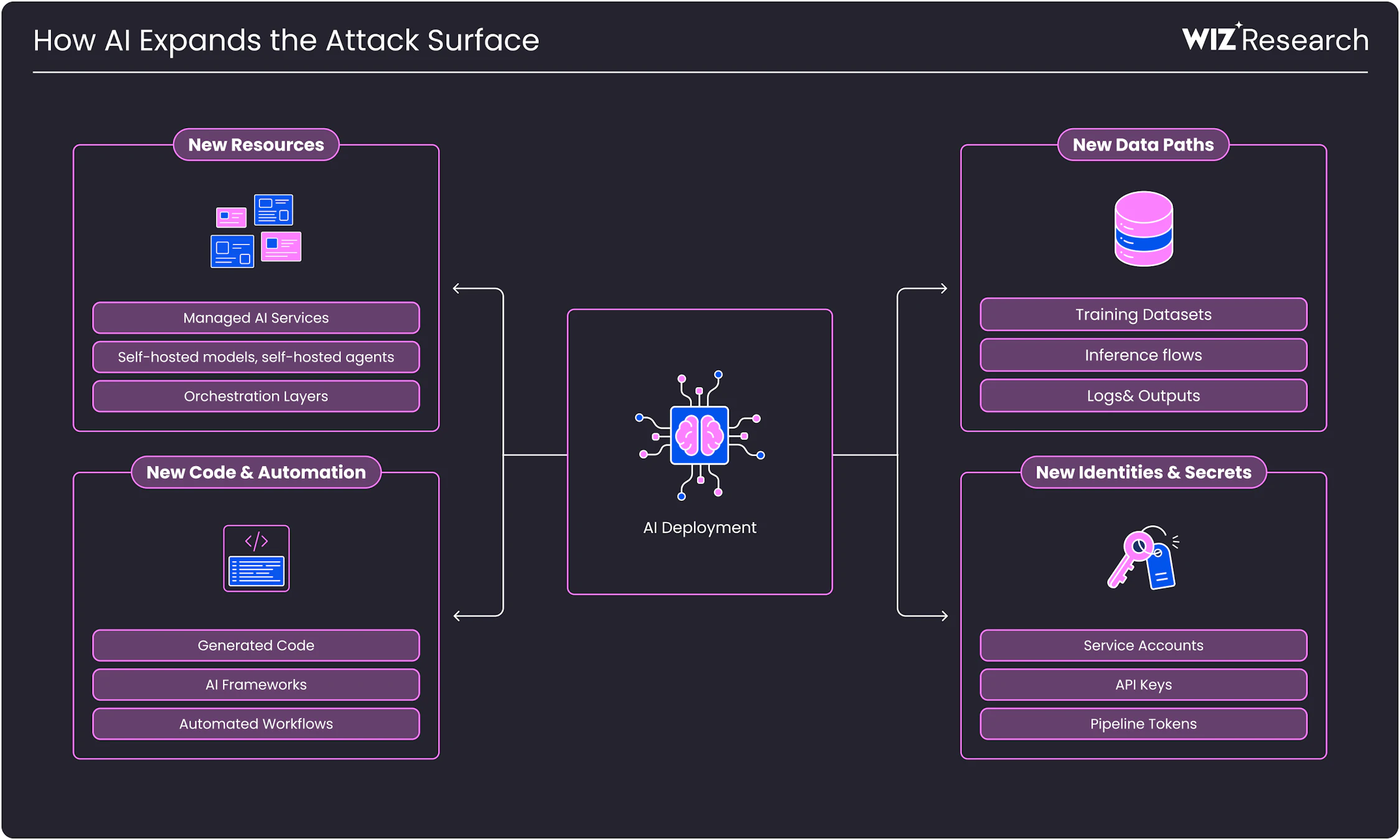
AI Is Expanding the Attack Surface

AI adoption is transforming how businesses operate—but it is also introducing new risks.What’s Changing:
More services and APIs
Increased number of identities and access points
New data flows and integrations
Automated workflows with elevated privilegesAI does not necessarily introduce entirely new vulnerabilities. Instead, it multiplies the environments where existing weaknesses can exist.
For example:
Misconfigured AI pipelines may expose sensitive datasets
Overprivileged AI services can become high-value targets
Automated processes can unintentionally propagate insecure configurationsThe result is a broader, more complex attack surface that is harder to monitor and secure.
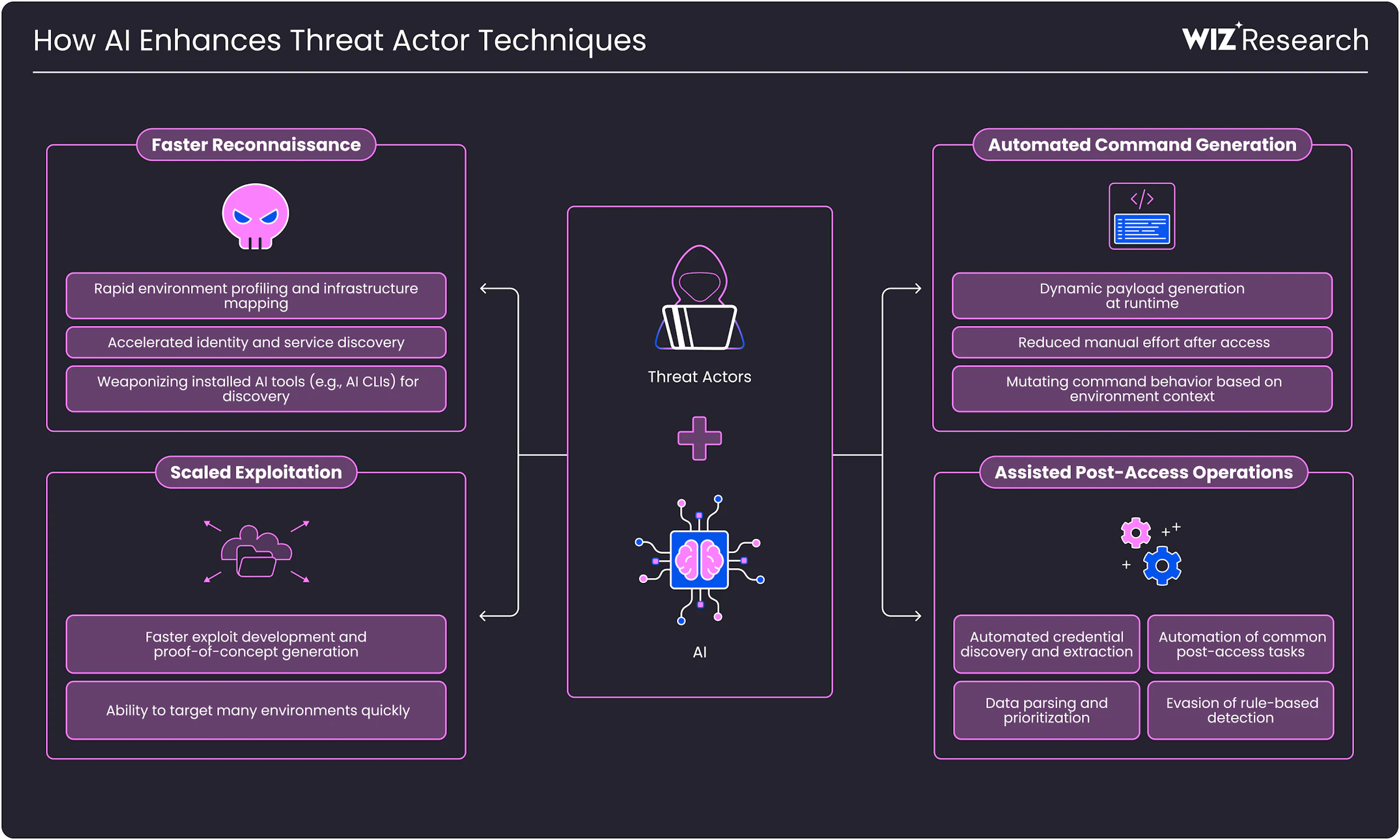
Threat Actors Are Using AI to Scale Attacks

Threat actors are not replacing traditional techniques with AI they are enhancing them.How AI Is Being Used:
Faster reconnaissance and data gathering
Automated scanning for vulnerabilities and misconfigurations
Scaling phishing, credential harvesting, and exploitation attemptsAI enables attackers to:
Reduce effort
Increase speed
Operate at scaleThis means even basic attack techniques can become significantly more dangerous when executed faster and across larger environments.
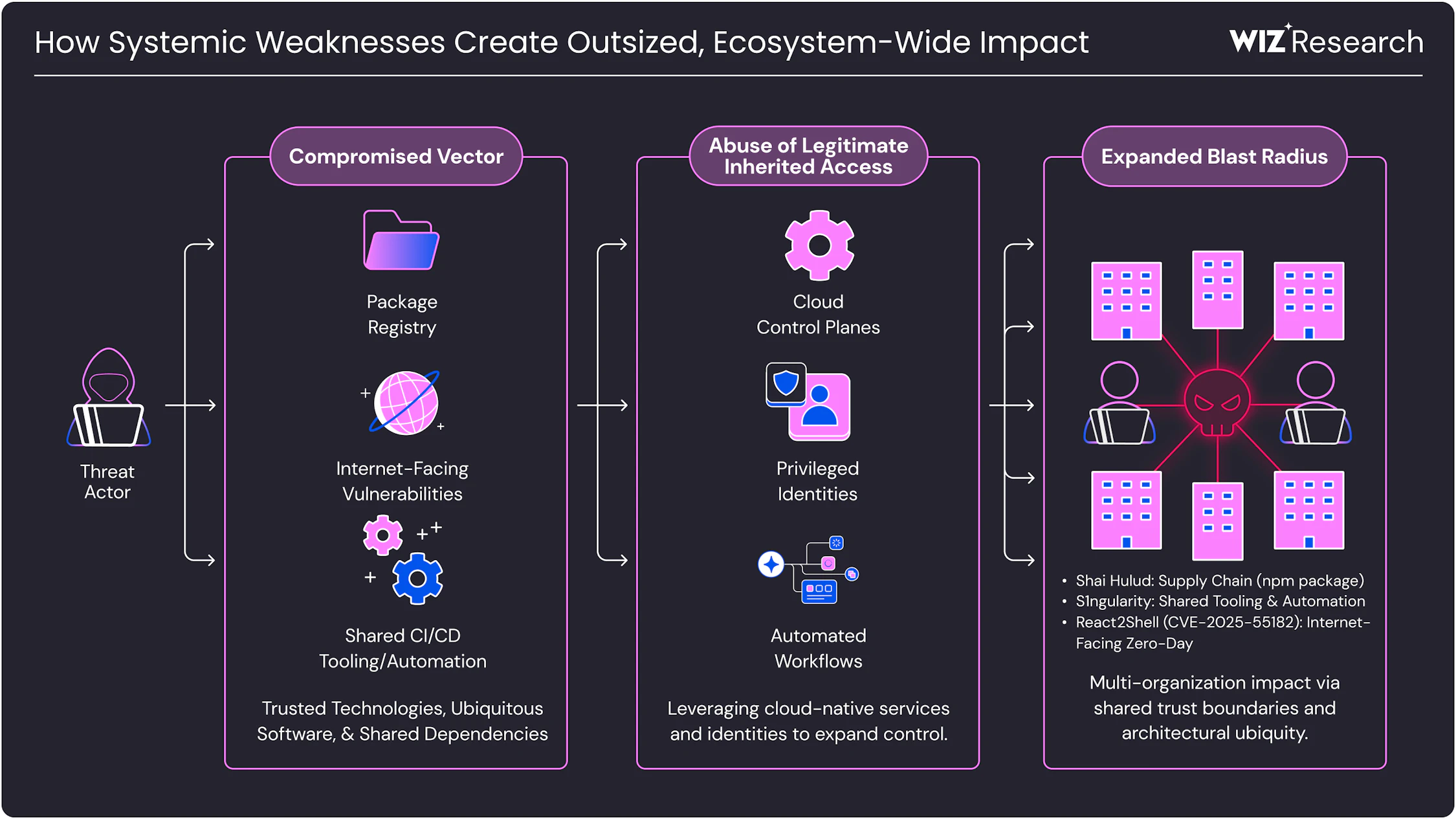
Systemic Weaknesses Lead to Larger Impact

One of the most important findings from the report is the role of systemic weaknesses.What Are Systemic Weaknesses?
These are vulnerabilities that exist across:
Shared software dependencies
Third-party integrations
Cloud-native services
Automation pipelinesWhen these components are compromised, the impact is no longer isolated.
Real-World Impact:
Incidents such as Shai-Hulud and React2Shell demonstrated how a single weakness in widely used components can cascade across multiple organizations.
This creates:
Supply chain risks
Widespread exposure
Large-scale incidents from a single point of failureIn modern cloud environments, trust relationships can become attack paths.
Key Takeaways for Security Teams
The report reinforces a critical shift in mindset:
Cloud security is no longer just about preventing intrusions it is about managing exposure at scale.Organizations Should Focus On:
1. Strengthening Security Fundamentals
Fix misconfigurations
Rotate and secure credentials
Patch known vulnerabilities2. Gaining Full Visibility
Monitor cloud assets, identities, and integrations
Track data flows and access patterns3. Managing Identity and Access
Enforce least privilege
Continuously review permissions4. Securing AI and Automation Layers
Audit AI pipelines and models
Monitor automated workflows5. Addressing Systemic Risk
Assess third-party dependencies
Evaluate trust relationships and integrations
Why This Matters More Than EverThe key takeaway from the Cloud Threats Retrospective 2026 is simple but powerful:
The biggest risks are not new they are just scaling faster and spreading wider.
Organizations that fail to address foundational security issues will continue to face breaches, regardless of how advanced their tools are.
At the same time, those that prioritize visibility, automation, and proactive risk management will be better positioned to defend against modern threats.
Final Thoughts
Cloud and AI technologies are reshaping the digital landscape but they are also amplifying existing security challenges.
The findings from Wiz highlight that security success depends less on chasing new threats and more on consistently addressing known risks at scale.
In today’s environment, resilience comes from:
Strong fundamentals
Continuous monitoring
Proactive security strategiesIf your organization is expanding its cloud and AI footprint, now is the time to reassess your security posture before familiar weaknesses turn into large-scale incidents.
- AuthorPosts
- You must be logged in to reply to this topic.